Make Us Your AR-VR Security Partner
AR or Augmented Reality technology is used to provide real experience environment for digitally created objects. Or it can defined as system comprising of aspects like combining real and virtual worlds and real time interaction of virtual objects which are perceived digitally.
AR Technology is just an extension of VR technology where instead of just giving virtual view of the real world, virtual objects are perceived as real world objects including interaction and accurate representation thus AR Technology is widely defined as ar-vr technology because of this inheritance.
It is mainly used to enhance natural environments or create real perception of virtual objects, such as video games or simulation environments.


How we help you
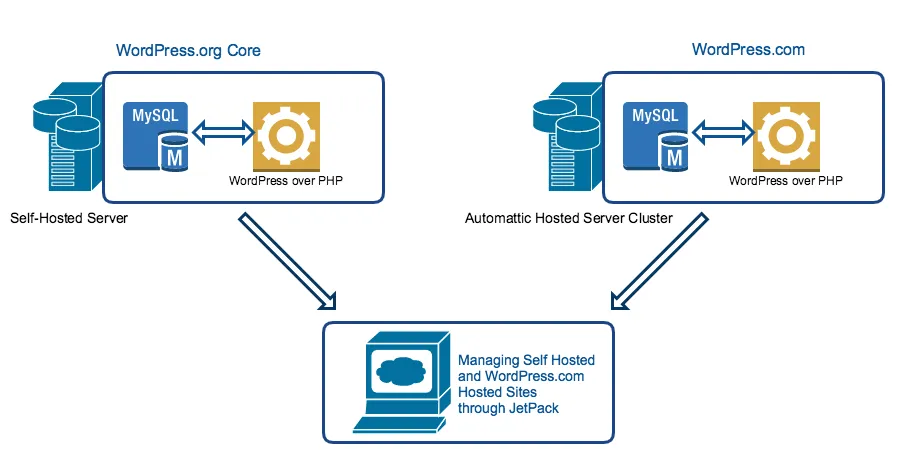
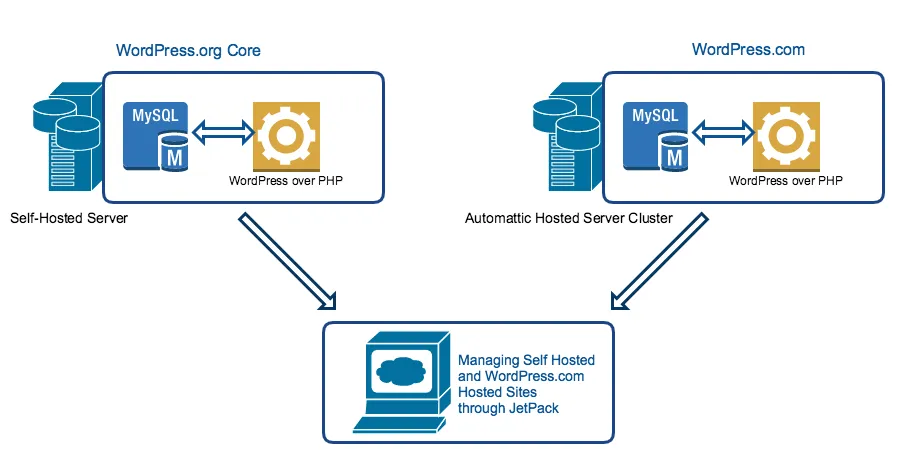
AR-VR Platform Architecture
- To use AR/VR technology, we need to have specialized hardware and a software platform to interpret virtual objects to augment into the real world, The platform should be able to map real world co-ordinates independent of camera images.
- Secondly, the platform will restore real world co-ordinates system based on the data collected and analysed from the previous step.
- The processing involves two main steps, firstly the software must identify interesting co-ordinates which represent the real object to be augmented and optical flow of the points to get overview of the object and its surroundings.
- AR Technology collects data through some mobile sensors to actively track the co-ordinates either through markers or markerless i.e, by identifying the geometry of the object by interpreting points, or by placing the object preferably in the view of the camera.
Empower your business with secure AR-VR
We understand your need to evolve, but evolution with security leads to success with lesser vulnerabilities.
Practices to Secure AR-VR Platform
- Use input sanitization policies – Since the AR Technology is based on gathering and analyzing user data, there must be some ways of filtering the data based on user preferences to protect privacy of user data. This is done using access control mechanism where users can control information accessible to the platform.
- Implement data privacy mechanisms – Some AR Platform collect data by crowdsourcing from search engines such as Google Search, there may be risk of data breach. So use some privacy algorithms that will aggregate data based on user preferences.
- Use biometric authentication for devices – Instead of using a single mode of authentication, use multi-modal biometric systems that combine two or more methods such as fingerprint and iris scanning to protect from shoulder-surfing attacks during authentication.
- Enable user-originating policies for protecting user interaction – Use some collaborative environments that manage multi-user interactions by using either vampire mirrors or privacy lamps, wherein privacy lamps that identifies private data by emitting light on interacting user or vampire lamps do this by reflecting objects using a mirror wherein public objects are opaque whereas private data is transparent or invisible.
Methods for Security Testing of AR-VR Platform
Since most of the data gathered by the AR/VR platforms is collaborative sourced from search engines try to modify the urls from which it sources its data since most of the attackers consider url modification as the most obvious attack vector.
How can we meet your Needs
Speak to a member of our leadership team today
AR-VR Platform Vulnerabilities
CVE-2019-9500
Remote code execution in Broadcom Bluetooth adapter of Microsoft hololens that allowed any unauthenticated attacker to perform denial of service attack.CVE-2018-16269
Whotil system service in Samsung Gear VR allowed any unprivileged attacker to exploit notifications data due to improper bus configurations.Explore How Invesics Can Become Your Digital Guard!
Find out from our cyber-security experts on a FREE consultation call